Organizing Committee
Brown University
Rutgers University
Microsoft Research India
Abstract
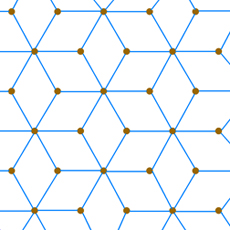
In the 1970's and 1980's lattices entered the world of cryptography as tools used to break certain crypto systems, particularly those based on the subset sum problem, and since the 1990's they have become increasingly important in the building of other types of crypto systems (thanks to the difficulty in the underlying mathematics). Their significance has recently been bolstered by average-case complexity bounds and their present resistance to quantum computing attacks.
Currently the theory of lattices is a lively research topic among mathematicians, computer scientists, and experts in cybersecurity. However, to this date, there has been little to no interaction between these communities. The goal of this workshop is to stimulate activity between these different groups interested in lattice problems. Topics to be covered include, but are not restricted to, recent results on densest lattice packings, the geometry of lattice moduli space and its connections with automorphic forms and algebraic number theory, cryptographic applications of lattices, and the state of the art of lattice reduction in high dimensions.
Loading participant list in background...